SOVERI Q1 2026 – Production Experience, Sovereignty Engineering, and 5 Years of the Internet Computer

At samlinux development group the first quarter of 2026 marked an important milestone for both SIM 3.0 and SOVERI. What initially started as a decentralized project management platform has increasingly evolved into a broader sovereignty focused infrastructure and operations layer running on the Internet Computer.
This article summarizes some of the most important operational learnings, architectural decisions, and strategic developments we have experienced while operating real production workloads on the European Subnet.
From Application to Sovereignty Platform
Over the last quarter, SIM 3.0 has matured significantly beyond a standalone application. Running production workloads continuously forces a shift in perspective: Infrastructure visibility, operational transparency, cost control, compliance considerations, and trust boundaries become just as important as application features themselves.
This operational evolution also strengthened the strategic meaning behind SOVERI. SOVERI is no longer simply the name of a project or application ecosystem. It is increasingly becoming a sovereignty-oriented operational and management layer for decentralized infrastructure and services running on the Internet Computer, with a strong focus on European digital sovereignty and GDPR aligned infrastructure.
This direction aligns closely with the emerging European discussion around sovereign cloud infrastructure and initiatives such as the European Commission’s Cloud Sovereignty Framework which aims to define measurable objectives for operational, legal, technological, and data sovereignty within Europe.
For us, sovereignty is not only about where infrastructure is hosted. It is about operational control, controllable trust boundaries, transparency, resilience, reducing dependency on hyperscalers, and maintaining long-term ownership of critical business systems and data within a European regulatory context.
Although achieving full data sovereignty remains challenging, even small steps towards greater sovereignty matter.
The Internet Computer provides a uniquely interesting foundation for this direction because applications, storage, and backend logic can operate directly on-chain without relying on traditional cloud servers or external databases.
Mission 70 and Operational Maturity
One of the defining ecosystem discussions during Q1 2026 was the publication of the Mission 70 initiative by the DFINITY Foundation.
The Mission 70 paper outlines a strategy to reduce ICP inflation by 70% by the end of 2026 while also discussing adjustments to the Internet Computer’s economic model and infrastructure pricing.
As expected, the community discussions around these proposals were intense and sometimes controversial. However, from our perspective, the most important effect was not the debate itself, but the operational questions it raised for real-world application operators.
The discussions immediately forced us to ask practical questions:
- How many cycles are we currently consuming?
- Which workloads are responsible for the highest operational costs?
- How does storage growth evolve over time?
- Which architectural decisions scale efficiently long-term?
This became the catalyst for significantly improving our operational observability.
By now, three versions of the Mission 70 paper have been published. The latest version is linked here: Mission70-2026-02-02.pdf
Building Sovereignty-Focused Monitoring
Until now, most of our production canisters on the European Subnet primarily consist of asset canisters hosting websites and product platforms.
Historically, cycle consumption was monitored through the linked canister panel available in the earlier NNS dapp experience. However, as the ecosystem evolved, it became clear that long-term production infrastructure requires much deeper operational visibility directly integrated into the application environment itself.
In hindsight, this turned out to be a very valuable development.
We began implementing our own integrated monitoring system directly inside SIM 3.0, transforming the platform into an operational management layer for all of our production canisters running on the Internet Computer.
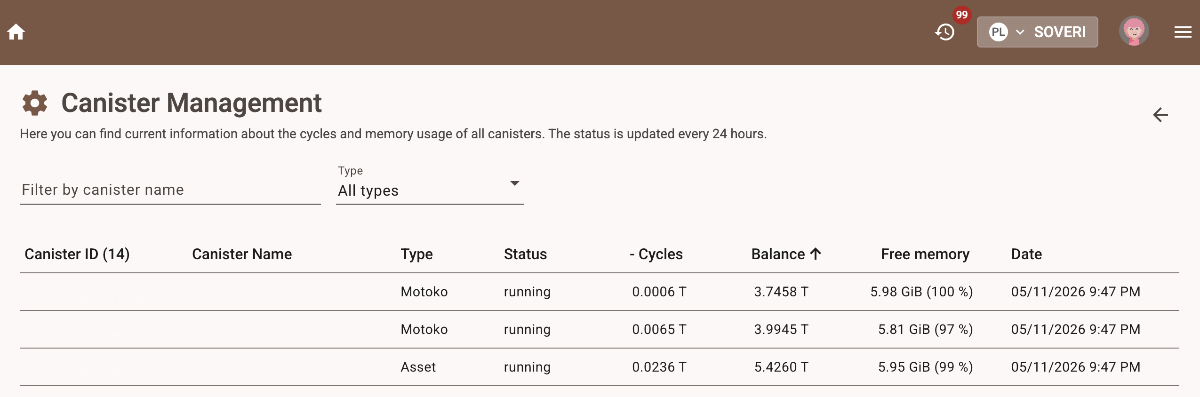
Today, we maintain visibility into:
- Cycle consumption
- Memory usage
This allows us to directly correlate infrastructure usage with real operating costs and continuously optimise our architecture based on measurable production data.
An especially important aspect for us was maintaining strict sovereignty over controller permissions.
On the Internet Computer, a canister controller has highly privileged access. Controllers are not only able to inspect operational data, but can also upgrade canisters, deploy new code, or modify critical settings.
For this reason, we have intentionally decided against relying on external monitoring providers that would require controller-level access to production systems.
From our perspective, sovereignty-focused infrastructure also means maintaining strict control over operational trust boundaries.
Understanding the Real Impact of Infrastructure Costs
One major topic raised during the Mission 70 discussions was the adjustment of storage pricing on the Internet Computer.
The approved motion proposal increased storage pricing from 4 SDR to 10 SDR per GiB per year, representing approximately a 2.5x increase in storage-related costs.
On the Internet Computer, cycles are pegged to the IMF’s SDR/XDR currency basket:
- 1 trillion cycles (1T cycles) = 1 XDR
- 1 XDR ≈ $1.35 USD
- approximately €1.24 EUR per 1 trillion cycles
This currently results in an estimated storage cost of approximately:
- ~ €12.40 per GiB/year
In practical terms, this remains manageable for our current production workloads, especially considering the operational and security characteristics provided by the Internet Computer architecture.
More importantly, our newly integrated monitoring infrastructure now allows us to make these evaluations based on real operational data instead of assumptions.
Interestingly, our findings also revealed that storage itself is not the most relevant cost factor in our production environment.
HTTP_OUTCALLS and Email Architecture Optimisation
One of the most valuable insights generated by our monitoring platform was related to email handling.
SIM 3.0 sends notifications to users and also imports operational customer emails into project workflows. Initially, outgoing emails were delivered directly through HTTP_OUTCALLS connecting to external mail services.
While technically functional, this approach introduced comparatively high cycle consumption for workloads that are typically considered inexpensive in traditional Web2 environments.
In addition, we observed consistent memory growth behavior associated with frequent HTTP_OUTCALL usage.
Rather than treating this as a limitation, we used it as an opportunity to redesign the architecture in a more operationally efficient and sovereignty-oriented way.
Queue-Based Email Delivery
Instead of sending emails directly from production canisters, we introduced a dedicated logging and queue canister architecture.
Outgoing emails are now stored as lightweight queue entries containing processing status information. An external service under our control periodically fetches pending emails, delivers them through the mail infrastructure, and updates their status afterward.
This approach delivered multiple advantages simultaneously:
- Dramatically reduced HTTP_OUTCALL usage
- Near-zero cycle costs for email delivery
- Lightweight audit and monitoring capabilities
- Better operational transparency
- Controlled storage growth
Query calls used for fetching pending emails are effectively free, while queue status updates inside the canister are comparatively inexpensive.
This architectural redesign significantly improved operational efficiency while maintaining full flexibility for future integrations.
GDPR-Aligned Email Importing
The second challenge involved importing customer emails into SIM 3.0 workflows.
Customer emails frequently contain:
- Personally identifiable information (PII)
- Embedded images
- Attachments
- Large HTML structures
- External content references
Persisting complete emails directly on-chain would not only increase storage consumption significantly, but would also introduce additional GDPR-related considerations.
As a result, we designed a hybrid architecture optimised for both sovereignty and operational efficiency.
Instead of storing complete emails directly on the Internet Computer, the original email content and attachments remain inside secure infrastructure under our own operational control.
Incoming emails are converted into PDF documents during the import process, providing a stable and visually consistent representation independent of mail clients or HTML rendering differences.
Within SIM 3.0 itself, we only store lightweight metadata references required to retrieve the corresponding document when needed.
This architecture provides several important advantages:
- Significantly lower storage consumption
- Reduced cycle costs
- Faster import performance
- Better control over GDPR-relevant data
- Reliable rendering consistency
- Reduced complexity for HTML email handling
The converted PDF documents can then be loaded on demand directly inside the SIM 3.0 frontend through an integrated PDF viewer.
From our perspective, this represents a pragmatic sovereignty-oriented architecture: sensitive customer communication remains under controlled infrastructure boundaries while the operational workflows and metadata continue running on-chain.
The Future of the European Subnet
The European Subnet has recently received increasing attention within the Internet Computer ecosystem.
One important development is the approved NNS proposal 139950, which plans to rename the “European Subnet” into the “EU/EEA Subnet”.
This reflects the fact that the subnet already includes infrastructure located within the broader European Economic Area and related regulatory landscape.
The transition is currently planned alongside the introduction of Trusted Execution Environment (TEE) functionality and a reduced subnet size of seven nodes.
For European organisations, this development is particularly interesting. It creates the foundation for infrastructure that combines:
- Sovereignty-oriented architecture
- European jurisdictional alignment
- Decentralized execution
- GDPR-focused operational models
- Stronger infrastructure transparency
As discussions around digital sovereignty, GDPR, NIS2, and strategic cloud independence continue accelerating across Europe, we believe the Internet Computer and the future EU/EEA subnet represent one of the most interesting emerging infrastructure models currently available.
Looking Forward
The market for sovereign cloud applications and sovereignty-focused infrastructure is growing rapidly across Europe.
At the same time, the broader Internet Computer ecosystem is increasingly expanding into sovereignty-focused cloud infrastructure initiatives for Europe.
One particularly interesting development is Cloud Engines on OpenCloud.org which aims to build sovereign cloud and collaboration services directly on the Internet Computer itself. This shows how the ecosystem is evolving beyond traditional blockchain applications towards real operational infrastructure for European organisations.
What makes this especially interesting is that initiatives like Cloud Engines run on the same decentralised infrastructure foundation as SIM 3.0 and SOVERI. The Internet Computer is increasingly positioning itself not only as a blockchain platform, but as a broader sovereign cloud infrastructure layer capable of hosting applications, collaboration systems, AI services, and enterprise workloads directly on decentralised infrastructure.
This direction aligns strongly with Europe’s growing focus on digital sovereignty, operational control, resilience, and reducing dependency on non-European hyperscaler ecosystems. Together with the future EU/EEA subnet and sovereignty-focused platforms such as SOVERI, initiatives like OpenCloud may become important building blocks for a new generation of European sovereign cloud infrastructure.
At samlinux development group, we are gaining practical production experience every day by operating real business applications on the Internet Computer and continuously optimising architecture, governance, operational transparency, and compliance considerations.
The past quarter has shown us that running sovereign infrastructure in production is not only technically possible, it also opens entirely new perspectives on operational ownership, trust models, and long-term infrastructure independence.
SOVERI continues to evolve in exactly this direction: From a decentralised application ecosystem into a sovereignty-focused operational platform built around real-world production experience on the Internet Computer.
If you are interested in exploring sovereign infrastructure, GDPR-aligned decentralised applications, or the Internet Computer ecosystem itself, feel free to get in touch with us.
 Home
Home  News & Insights
News & Insights  Product Suite
Product Suite  Deck
Deck  About
About  Imprint
Imprint  Data Privacy
Data Privacy 


